Financial institutions are currently facing a massive surge in illicit transactions facilitated by unsuspecting or complicit individuals acting as intermediaries. The specific case involving coordinated recruitment through social media highlights how criminal organizations exploit the perceived legitimacy of private bank accounts to bypass traditional monitoring systems. Authorities have recently intensified their focus on these decentralized networks, leading to significant enforcement actions and the imposition of a 5 million euro fine against a major payment processor for systemic failures in detecting these patterns. This enforcement action underscores the urgent necessity for robust digital verification and real-time transaction monitoring to prevent the layering of criminal proceeds. The following analysis explores the mechanics of these schemes and the regulatory response required to mitigate the evolving risks of financial crime.
Table of Contents
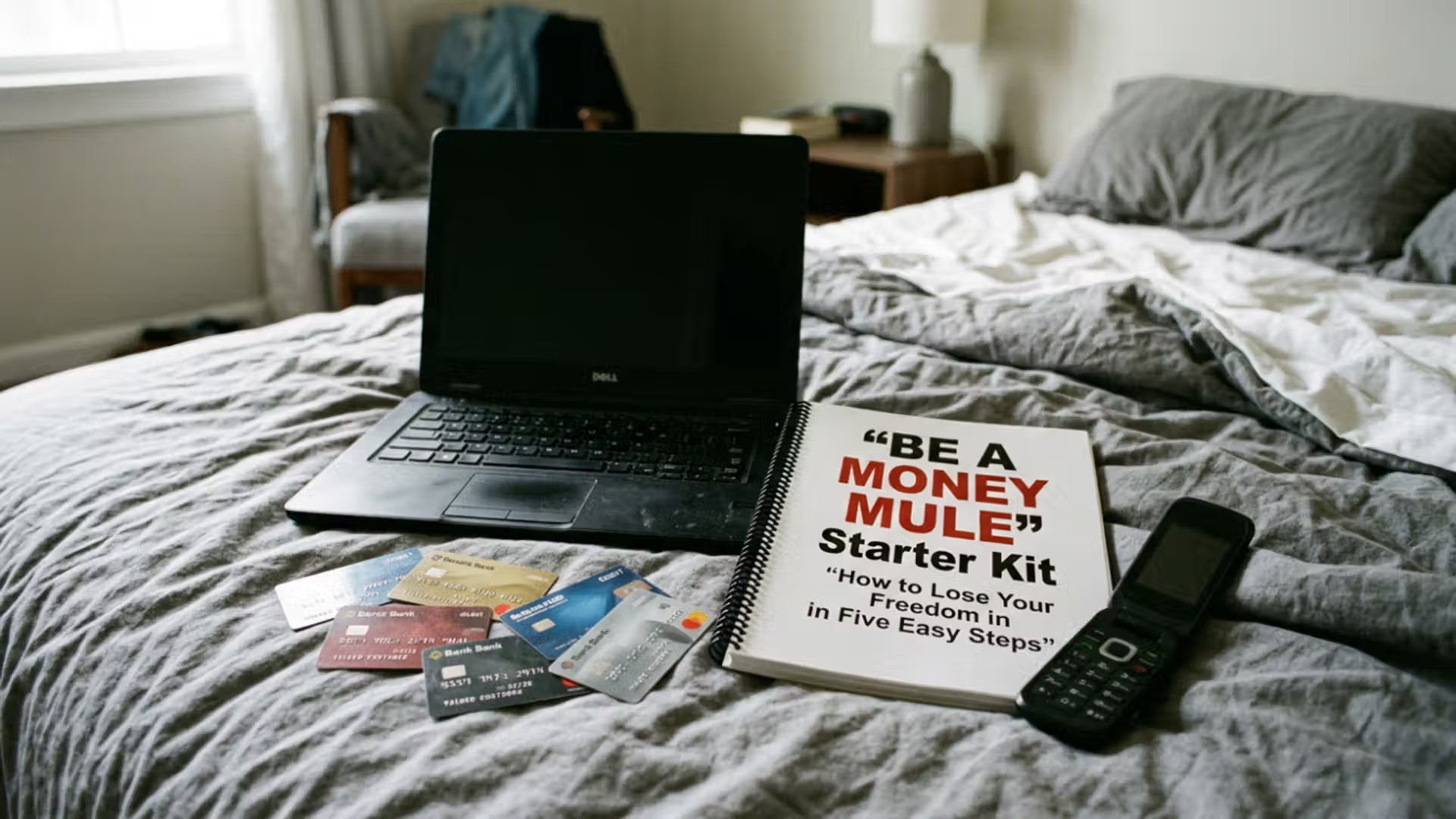
Money Mule Recruitment Tactics and Financial Exploitation
The core of the money mule phenomenon lies in the deceptive recruitment strategies used by international criminal syndicates to find individuals willing to move illicit funds. Often, these recruiters target younger demographics or those seeking remote work opportunities through social media platforms, promising high returns for minimal effort. The process typically begins with a job advertisement for a financial manager or a local payment agent, where the primary responsibility is to receive transfers into a personal bank account and then forward the balance to another account, often located in a different jurisdiction. This method is effective because it creates a fragmented audit trail that is difficult for a single institution to piece together. By using thousands of individual accounts across various banks, criminals ensure that no single transaction is large enough to trigger immediate high-level scrutiny, effectively hiding the movement of massive sums of money in plain sight.
The financial impact of these networks is profound, as they serve as the primary exit ramp for proceeds from cybercrime, phishing, and investment fraud. When an individual agrees to participate, they often do not realize they are participating in a felony, yet the legal consequences remain severe regardless of intent. Regulators have noted that the rapid digitisation of banking services has provided a fertile ground for these activities to flourish. Traditional anti-money laundering frameworks, which were designed to detect large cash deposits or high-value wire transfers, are often ill-equipped to handle the high velocity of small, peer-to-peer transfers that characterize mule activity. This gap in oversight has allowed syndicates to move millions of euros before a single account is flagged and frozen.
Furthermore, the psychological manipulation involved in recruitment cannot be understated. Recruiters often build a sense of trust or urgency, making the victim feel like they are part of a legitimate business operation. In some instances, the mules are themselves victims of romance scams, where the promise of a future relationship is used as leverage to convince them to move money. This intersection of fraud and money laundering creates a complex legal landscape where the line between victim and perpetrator becomes blurred. However, from a regulatory standpoint, the account holder is responsible for the activity occurring within their personal financial space, making the education of the public a critical component of any national anti-money laundering strategy.
Structural Vulnerabilities in Global Payment Processing
Digital payment processors and neo-banks have revolutionized the speed of commerce, but they have also introduced structural vulnerabilities that money mule networks are quick to exploit. The case at hand demonstrates how a lack of stringent know-your-customer protocols at the onboarding stage can lead to catastrophic failures. When a payment processor prioritizes rapid user growth over rigorous compliance checks, they essentially provide a low-friction environment for criminal activity. The 5 million euro fine mentioned previously serves as a landmark warning to the industry that speed must not come at the expense of security. These institutions are now under pressure to implement advanced behavioral analytics that can distinguish between legitimate consumer behavior and the mechanical patterns of a money mule.
A key challenge for compliance officers is the sheer volume of data generated by modern payment systems. Unlike traditional banking, where a customer might have a long-term relationship with a branch, digital-first users are often anonymous and transitory. This anonymity is a primary driver for the mule industry. Criminals look for platforms with weak geographic restrictions and automated approval processes. Once a cluster of accounts is established, they can be used for a burst of activity known as rapid-fire laundering, where funds are moved through dozens of accounts in a matter of minutes. This velocity makes it nearly impossible for manual review teams to intervene before the money is converted into cryptocurrency or withdrawn at an automated teller machine in a high-risk jurisdiction.
To combat this, international bodies like the Financial Action Task Force have called for greater information sharing between the public and private sectors. The compartmentalization of financial data is a significant hurdle, as privacy laws sometimes prevent banks from warning each other about suspicious account holders in real-time. However, the emergence of shared blacklists and collaborative platforms is beginning to turn the tide. By identifying the unique digital fingerprints of mule recruiters, such as specific IP addresses or device identifiers, institutions can proactively block the creation of new accounts. The goal is to move from a reactive posture to a predictive one, where the network is dismantled at the recruitment phase rather than after the funds have already vanished.
Regulatory Evolution and the Future of Financial Integrity
The evolving nature of financial crime requires a corresponding evolution in the legal and regulatory frameworks that govern the industry. The case study of the large-scale mule network illustrates that local enforcement is no longer sufficient; a global, coordinated approach is mandatory. Law enforcement agencies are increasingly using sophisticated data mining tools to trace the flow of funds across borders, leading to the successful prosecution of high-level organizers rather than just the low-level mules. These investigations often reveal that the money laundered through these schemes is directly linked to more sinister activities, including human trafficking and the financing of organized crime groups. By cutting off the financial lifeblood of these organizations, authorities can effectively disrupt their operational capabilities.
Legislative updates in many jurisdictions are now moving toward holding financial institutions more strictly accountable for the actions of their users. The concept of failure to prevent money laundering is becoming a standard legal doctrine, placing the burden of proof on the institution to show they had adequate safeguards in place. This shift has led to a surge in investment in regulatory technology, with firms spending billions on artificial intelligence and machine learning to bolster their defenses. These technologies are capable of analyzing vast datasets to identify subtle anomalies that would be invisible to the human eye, such as a sudden change in the typical transaction frequency or geographical location of a previously dormant account.
In the long term, the fight against money mule networks will depend on a combination of technology, regulation, and public awareness. Education campaigns aimed at vulnerable populations can reduce the supply of potential mules, while stricter enforcement can increase the risk for the orchestrators. The 5 million euro penalty is just one example of the increasing costs of non-compliance. As the financial landscape becomes even more interconnected through the rise of decentralized finance and instant payment rails, the complexity of the task will only grow. However, the lessons learned from recent cases provide a clear roadmap for the future: transparency, rapid communication, and an unwavering commitment to financial integrity are the only ways to safeguard the global economy from the predatory tactics of modern money launderers.
Money Mule Identification Typologies
The identification of money mule activity requires a nuanced understanding of behavioral and transactional patterns that deviate from standard retail banking norms. AML professionals should prioritize the following indicators when reviewing account activity to detect potential mule involvement.
- Rapid Circular Movement: The account receives a large credit from an unknown source and immediately transfers the exact amount, minus a small commission, to a third party or a cryptocurrency exchange.
- Dormancy Followed by High Velocity: A personal account that has been inactive for several months suddenly experiences a high volume of transactions, often just below the mandatory reporting thresholds.
- Geographic Mismatch: Transactions originate from or are sent to high-risk jurisdictions that have no logical connection to the account holder’s stated occupation or residency.
- Social Media Recruitment Footprints: Account holders are unable to provide legitimate documentation for the source of funds, often citing vague employment contracts or online work discovered through encrypted messaging apps.
- Multiple Account Linkage: Several seemingly unrelated accounts share the same login IP address, device ID, or physical mailing address, suggesting a centralized control hub.
Key Points
- A significant 5 million euro fine was issued to a payment processor for failing to prevent the exploitation of its platform by money mule networks.
- Money mule recruitment heavily relies on social media and deceptive job advertisements to target vulnerable individuals for illicit fund transfers.
- Modern money laundering schemes utilize high-velocity transactions across thousands of personal accounts to evade traditional detection systems.
- Global regulatory bodies are shifting toward a failure to prevent model, increasing the legal and financial liability for non-compliant institutions.
Related Links
- FATF Report on Money Laundering through Money Mules
- Europol Action Against Money Muling Networks
- EBA Guidelines on Internal Governance and AML Compliance
- FinCEN Advisory on Illicit Financial Activity and Recruitment
Other FinCrime Central Articles About Money Mules
- Cross-Border Money Mule Rings Under Pressure
- The Rise of Mule Accounts as a Service (MAaaS): A Growing Underground Economy
- Chinese Mafia Behind Plane Full of Money Mules Busted in Major Operation
Source: Interesting podcast on this on FMA
Some of FinCrime Central’s articles may have been enriched or edited with the help of AI tools. It may contain unintentional errors.
Want to promote your brand, or need some help selecting the right solution or the right advisory firm? Email us at info@fincrimecentral.com; we probably have the right contact for you.