Category: Technology
The Growing Threat of Synthetic Identity Fraud and Automated Liveness Bypasses
Financial networks face escalating challenges as automated synthetic identity, deepfake tools and virtual camera injections compromise traditional biometric verification pipelines. Discover the core AML typologies required to protect modern onboarding systems.
Read MoreModel Collapse Risks Are Emerging Inside AML AI Systems
Model collapse is becoming a serious concern for AML teams as synthetic compliance datasets and AI-generated investigative content increasingly contaminate financial crime machine learning systems.
Read MoreCriminal Networks Quietly Deploy AI Before Banks Catch Up
AI laundering detection is becoming critical as criminal networks deploy synthetic identities, deepfake onboarding, fake source of funds records, and AI powered mule recruitment against financial institutions.
Read MoreMT103 Fields Explained for AML Monitoring and Risk Detection
MT103 AML analysis is critical for detecting suspicious wire transfers, helping compliance teams interpret transaction data, identify red flags, and meet regulatory expectations.
Read MoreShifting Legal Landscapes: Navigating Jurisdictional Drift in AML Compliance
Maintaining jurisdictional requirements in AML systems is critical as legislative nuances shift, requiring proactive identification and adjustment of monitoring logic to ensure global compliance integrity.
Read More
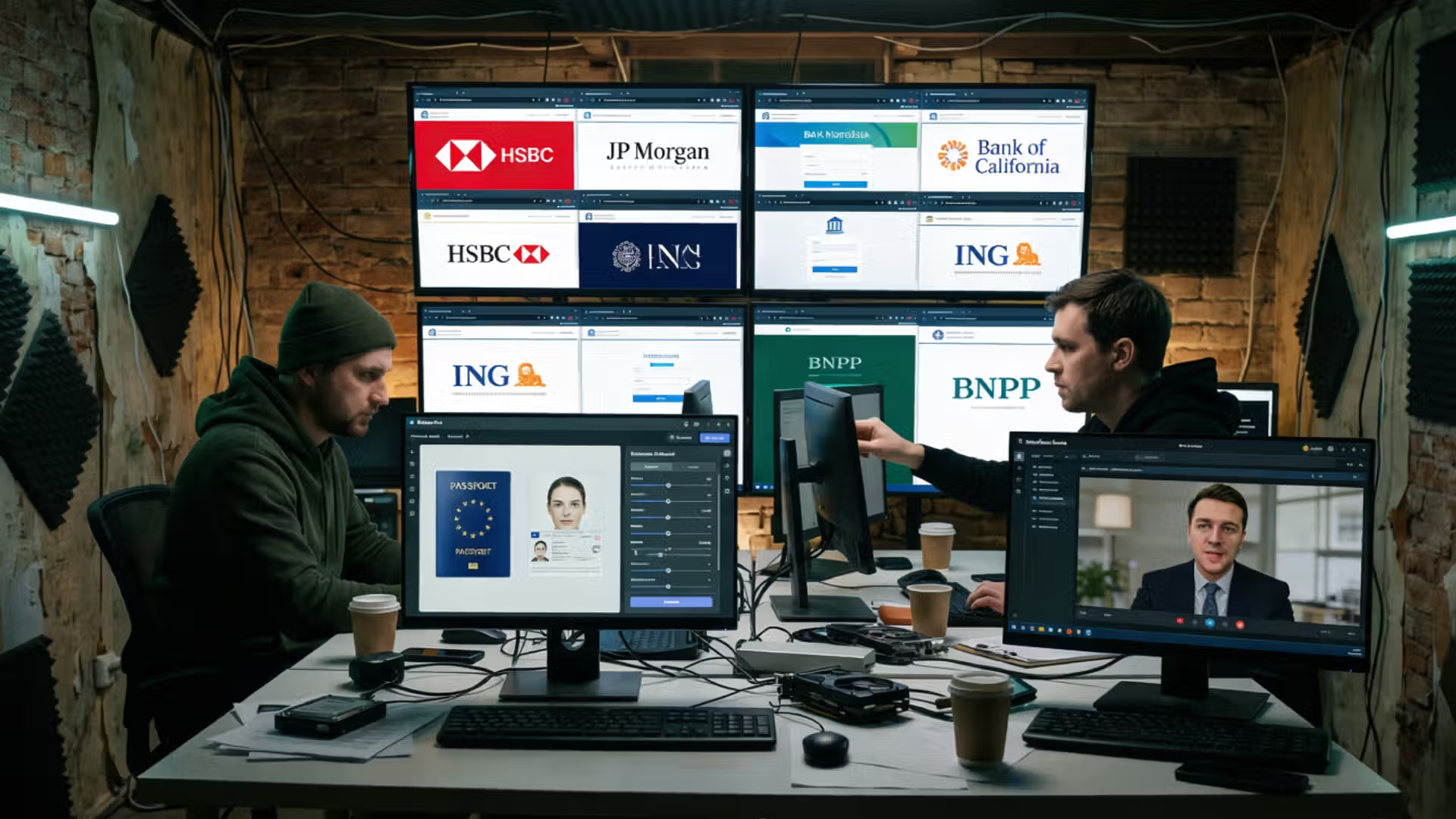
The Growing Threat of Synthetic Identity Fraud and Automated Liveness Bypasses
Financial networks face escalating challenges as automated synthetic identity, deepfake tools and virtual camera injections compromise traditional biometric verification pipelines. Discover the core AML typologies required to protect modern onboarding systems.
Read MoreModel Collapse Risks Are Emerging Inside AML AI Systems
Model collapse is becoming a serious concern for AML teams as synthetic compliance datasets and AI-generated investigative content increasingly contaminate financial crime machine learning systems.
Read MoreCriminal Networks Quietly Deploy AI Before Banks Catch Up
AI laundering detection is becoming critical as criminal networks deploy synthetic identities, deepfake onboarding, fake source of funds records, and AI powered mule recruitment against financial institutions.
Read MoreMT103 Fields Explained for AML Monitoring and Risk Detection
MT103 AML analysis is critical for detecting suspicious wire transfers, helping compliance teams interpret transaction data, identify red flags, and meet regulatory expectations.
Read MoreShifting Legal Landscapes: Navigating Jurisdictional Drift in AML Compliance
Maintaining jurisdictional requirements in AML systems is critical as legislative nuances shift, requiring proactive identification and adjustment of monitoring logic to ensure global compliance integrity.
Read More
The Growing Threat of Synthetic Identity Fraud and Automated Liveness Bypasses
Financial networks face escalating challenges as automated synthetic identity, deepfake tools and virtual camera injections compromise traditional biometric verification pipelines. Discover the core AML typologies required to protect modern onboarding systems.
Read MoreModel Collapse Risks Are Emerging Inside AML AI Systems
Model collapse is becoming a serious concern for AML teams as synthetic compliance datasets and AI-generated investigative content increasingly contaminate financial crime machine learning systems.
Read MoreCriminal Networks Quietly Deploy AI Before Banks Catch Up
AI laundering detection is becoming critical as criminal networks deploy synthetic identities, deepfake onboarding, fake source of funds records, and AI powered mule recruitment against financial institutions.
Read MoreMT103 Fields Explained for AML Monitoring and Risk Detection
MT103 AML analysis is critical for detecting suspicious wire transfers, helping compliance teams interpret transaction data, identify red flags, and meet regulatory expectations.
Read MoreShifting Legal Landscapes: Navigating Jurisdictional Drift in AML Compliance
Maintaining jurisdictional requirements in AML systems is critical as legislative nuances shift, requiring proactive identification and adjustment of monitoring logic to ensure global compliance integrity.
Read More