An exclusive article by Fred Kahn
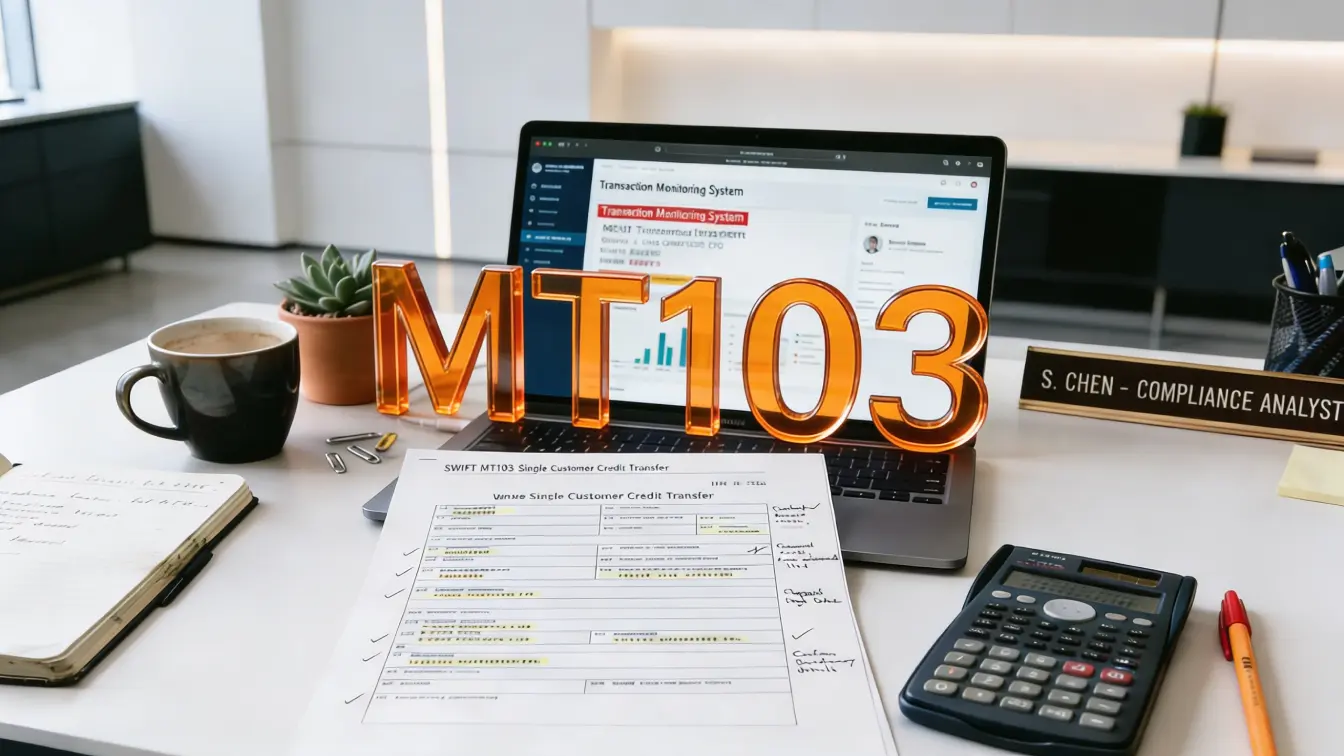
Cross-border payments remain one of the highest risk channels for financial crime, and the MT103 message sits at the centre of this activity. What follows is a practical guide to understanding MT103 messages, how their structure works, and which elements AML specialists must review to detect risk. Supervisory bodies such as the Financial Action Task Force and European regulators expect institutions to demonstrate clear control over payment data. A structured understanding of each field allows analysts to connect transaction details with customer risk and monitoring logic. This knowledge is essential for identifying suspicious activity and meeting regulatory expectations.
Table of Contents
Understanding MT103 structure for AML specialists
The MT103 message is a standardized SWIFT format used to execute single customer credit transfers between financial institutions. It contains multiple structured fields that together form a complete payment instruction. For AML professionals, this structure provides both an opportunity and a challenge, as each field must be interpreted within the broader context of customer behaviour and institutional risk.
Field 20 contains the transaction reference number. This identifier is critical for tracing payment flows across systems and linking alerts to specific transfers. While it does not directly indicate risk, it enables investigators to reconstruct transaction chains, which is essential in complex laundering schemes involving multiple transfers.
Field 23B defines the operation code, typically indicating a standard credit transfer. Deviations from expected codes may indicate unusual processing or special instructions that warrant closer scrutiny. Although often overlooked, this field can reveal inconsistencies between the declared transaction type and the underlying activity.
Field 32A includes the value date, currency, and amount. This field is central to monitoring for structuring and unusual transaction patterns. Repeated transfers just below reporting thresholds or amounts inconsistent with a customer’s profile are common indicators of suspicious activity. The timing of transactions, especially when funds move rapidly across accounts, is also a key signal.
Field 50 identifies the ordering customer. This is one of the most critical elements for AML analysis. The information provided must align with the institution’s customer due diligence records. Incomplete or inconsistent details may indicate attempts to obscure the true origin of funds. Variations in naming conventions, addresses, or identification numbers require careful review.
Field 59 contains the beneficiary customer information. Similar to the ordering customer field, it must be consistent with expected recipient profiles. Payments to unrelated third parties, especially in high-risk jurisdictions, may indicate layering or integration stages of money laundering.
Field 70 provides the payment narrative. This free text field is frequently exploited due to its flexibility. Generic descriptions, such as services or consulting, offer little transparency and may be used to disguise the true purpose of a transaction. AML specialists must evaluate whether the narrative aligns with the customer’s known business activities.
Field 71A specifies the details of charges. While primarily operational, unusual arrangements regarding who bears the transaction costs may signal attempts to manipulate payment flows or obscure economic intent.
Together, these fields form a comprehensive dataset that allows institutions to assess transaction risk. However, the value of this data depends entirely on how well it is integrated into monitoring systems and interpreted by analysts.
Key red flags hidden in transaction data
Effective AML monitoring requires identifying patterns rather than isolated anomalies. The MT103 message provides multiple indicators that, when combined, can reveal suspicious behaviour.
One of the most common red flags is inconsistency between customer profiles and transaction activity. A low-risk retail customer sending large international transfers to corporate beneficiaries without a clear economic rationale should trigger further investigation. Similarly, sudden changes in transaction behaviour, such as increased frequency or volume, may indicate account misuse.
Geographical risk is another critical factor. Payments involving jurisdictions identified as high risk by international bodies require enhanced scrutiny. Routing transactions through multiple intermediary banks located in different regions may suggest attempts to obscure the origin or destination of funds.
The use of intermediaries is particularly relevant in correspondent banking. Fields related to intermediary institutions can reveal complex routing structures. While legitimate in many cases, unnecessarily complicated paths may indicate layering strategies designed to make tracing funds more difficult.
Free text manipulation in the payment narrative remains a persistent challenge. Criminals may use vague descriptions, abbreviations, or deliberately misleading information. Advanced monitoring systems often incorporate keyword analysis, but human review remains essential to interpret context accurately.
Another important indicator is repetitive transaction patterns. Multiple payments of similar amounts sent within short timeframes can signal structuring. When combined with different beneficiaries or slight variations in details, these patterns may indicate attempts to avoid detection thresholds.
Timing also plays a role. Rapid movement of funds, particularly when incoming and outgoing transfers occur within a short period, can suggest layering. This behaviour is often seen in accounts used as pass-through vehicles.
Linking transaction monitoring to regulatory expectations
Regulators expect financial institutions to demonstrate a clear link between risk assessments and monitoring controls. The MT103 message is a primary data source for fulfilling these expectations.
The Financial Action Task Force requires that wire transfers include accurate and meaningful originator and beneficiary information. This requirement is reflected in international standards and national regulations. Institutions must ensure that the data contained in MT103 messages is complete and verified.
European regulations, including the EU framework on fund transfers, mandate transparency in payment information. Missing or incomplete fields can result in regulatory breaches and enforcement actions. Institutions are required to implement controls that detect and address such deficiencies.
Transaction monitoring systems must be configured to capture relevant risk indicators from MT103 fields. This includes setting thresholds for unusual activity, defining scenarios for high-risk jurisdictions, and ensuring that alerts are generated when predefined conditions are met.
Documentation plays a critical role. Regulators not only assess whether monitoring systems exist, but they also evaluate whether institutions can explain how these systems are configured. Each threshold, scenario, and rule must be justified and linked to the institution’s risk assessment.
Failure to establish this link has been a recurring issue in enforcement actions. Institutions may have advanced technology in place, but without a documented methodology explaining how MT103 data drives monitoring decisions, the programme is considered deficient.
Building practical review workflows for analysts
A structured approach to reviewing MT103 messages can significantly enhance detection capabilities. AML analysts should follow a consistent workflow that integrates both automated alerts and manual assessment.
The first step is validating the completeness and consistency of key fields. Analysts should confirm that the originator and beneficiary information aligns with internal records. Any discrepancies should be escalated for further review.
Next, the transaction context must be assessed. This includes evaluating the purpose of the payment, the relationship between parties, and the economic rationale. The payment narrative should be examined in conjunction with customer profiles to determine plausibility.
Geographical factors should then be considered. Transactions involving high-risk jurisdictions or unusual routing patterns require additional scrutiny. Analysts should assess whether the involvement of intermediary banks is justified.
Pattern analysis is also essential. Reviewing historical transaction data can reveal whether the current payment fits within expected behaviour. Deviations from established patterns should be treated as potential indicators of risk.
Finally, documentation of findings is critical. Analysts must record the rationale behind their decisions, including why a transaction was deemed suspicious or not. This documentation supports internal governance and provides evidence during regulatory examinations.
Strengthening control through structured analysis
Effective AML monitoring depends on the ability to interpret structured payment data within a broader risk framework. The MT103 message provides a detailed view of transaction activity, but its value is realized only when institutions apply consistent and well-documented analysis.
A strong approach combines automated detection with expert judgment. Systems can identify patterns and flag anomalies, but human analysis is required to understand context and intent. This balance is essential for accurate risk assessment.
Institutions that invest in training and methodology development are better positioned to meet regulatory expectations. Analysts must understand not only how to read MT103 fields, but also how these fields relate to customer risk, business activity, and regulatory requirements.
Continuous review and improvement are necessary. As financial crime risks evolve, monitoring frameworks must adapt. This includes updating scenarios, refining thresholds, and ensuring that methodologies remain aligned with current risks.
The MT103 message will continue to play a central role in AML efforts. Its structured format provides a reliable foundation for monitoring, but only when supported by a coherent and defensible framework. Institutions that achieve this alignment can move beyond reactive compliance and build a more resilient approach to financial crime risk.
Key Points
- MT103 messages provide structured data essential for detecting suspicious transactions in cross-border payments
- Critical fields such as originator, beneficiary, and narrative must align with customer profiles and expected activity
- Red flags include unusual routing, vague payment purposes, and repetitive transaction patterns
- Regulators require clear linkage between risk assessments and how MT103 data is used in monitoring systems
- Effective AML control depends on combining automated systems with structured analyst review workflows
Related Links
- FATF Recommendation 16 Wire Transfers
- European Commission Regulation on Information Accompanying Transfers of Funds
- SWIFT MT103 Message Structure Overview
- FCA Guidance on Financial Crime Systems and Controls
- EBA Guidelines on Risk Factors for AML CFT
Other FinCrime Articles About Payments
- BIS Report Demands Consistent Regulatory Approach for Global Payments
- The European Payments Council Advances Central Fraud Information Sharing
- Inside FATF’s Revised R.16 That Redefines AML Compliance for Payments
Some of FinCrime Central’s articles may have been enriched or edited with the help of AI tools. It may contain unintentional errors.
Want to promote your brand, or need some help selecting the right solution or the right advisory firm? Email us at info@fincrimecentral.com; we probably have the right contact for you.