An exclusive article by Mohan Paranthamam
Financial institutions have spent the last decade pouring money into AML/CFT technology: transaction monitoring engines, screening databases, KYC onboarding platforms, and case management systems. Yet when regulators open a file, the most consistently cited deficiency is almost never the technology itself. It is something more fundamental, and far harder to buy off the shelf.
It is the methodology layer, the documented, institution-specific framework that explains why every risk was identified, why every threshold was set, and why every control exists. It is the brain of the compliance programme. And in most institutions, it is missing. When examiners arrive, whether under BaFin’s §44 KWG, the FCA’s SYSC regime, FinCEN’s BSA/AML examination manual or MAS Notice 626, they don’t just ask what the bank did. They ask why. In the absence of a coherent methodology, even the most sophisticated AML stack cannot answer that question.
Table of Contents
Every Audit, Same Finding
The methodology gap is not a German problem, nor a European one. In a review of BaFin §44 examination findings between 2022 and 2025, inadequate or absent AML/CFT risk methodology documentation was the single most frequently cited deficiency at mid-tier institutions. The same pattern appears elsewhere: the FCA’s 2023 AML thematic review flagged “inadequate firm-wide risk assessment” in the majority of firms reviewed; OCC consent orders from 2020–2025 repeatedly require remediation of the risk assessment before any other programme improvement; MAS and FINMA have surfaced the same structural gap in their respective thematic inspections.
The recent enforcement record sharpens the point. BaFin’s €45 million fine against J.P. Morgan SE in October 2025 for systemic delays in submitting suspicious transaction reports was, at root, not a technology failure. The alerts were generated. What was missing was a documented framework specifying the escalation path, the accountable roles at each stage, and the maximum elapsed time between alert and report. N26, Solaris, Commerzbank, and UmweltBank all tell variations of the same story: operational systems not tethered to a documented methodology that explains how they are meant to work, at what threshold, and under what governance.
The FCA’s £264.8 million criminal fine against NatWest and the £107.7 million penalty against Santander UK point the same way. In each case, the customer risk model was unable to flag behaviour that diverged dramatically from what the model predicted, because the link between the risk assessment and the monitoring configuration had never been documented.
The central finding: regulators are not judging compliance programmes on their components. They are judging them on whether the components are held together by a defensible framework. Where that framework is absent, the programme is, in regulatory terms, unexplainable and therefore indefensible.
We have seen this firsthand. In every mid-tier institution we have worked with, the same pattern holds: the technology stack is mature, the policy binder is thick, and the MLRO still cannot answer, without hedging, why a specific customer risk threshold was set at the level it was. The uncomfortable truth is that most compliance programmes are operationally capable but intellectually hollow. They can run. They cannot explain themselves.
What the Methodology Layer Actually Is
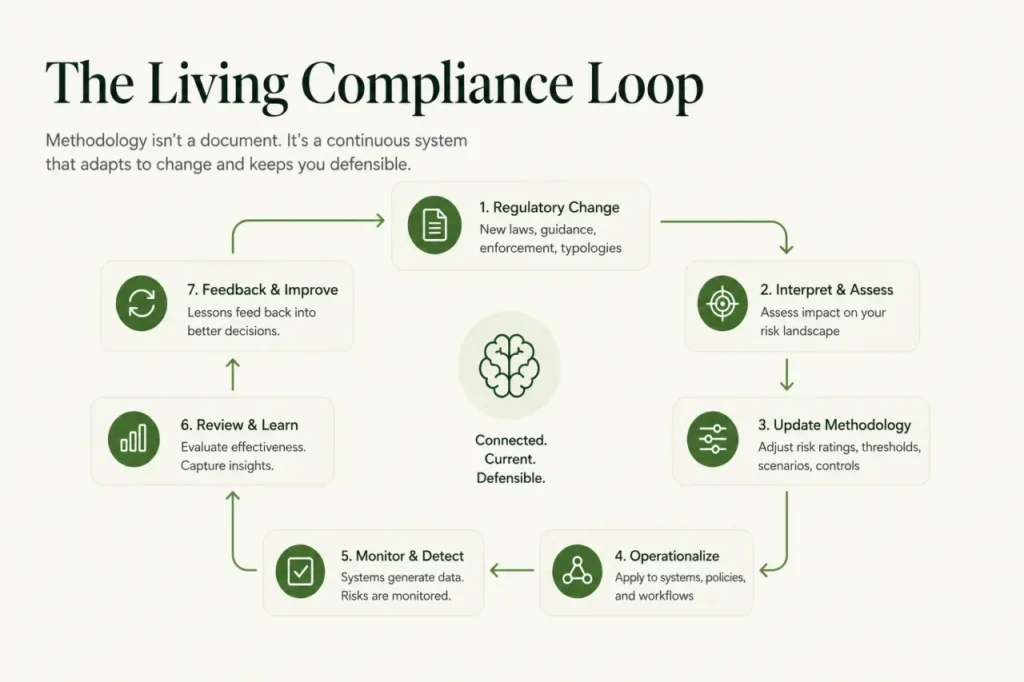
The methodology is not the policy. Policies describe what an institution will do; the methodology explains why. It is also not the compliance manual, which is the operational execution guide. The methodology sits above both as the intellectual foundation of the programme.
A complete methodology layer connects several interdependent components:
- Business reality assessment: an institution-specific mapping of products, services, customer segments, geographies and delivery channels, with risk ratings applied to each.
- ML and TF risk assessments: structured and crucially separate, analyses of money laundering and terrorist financing exposure. Separation of TF is already mandatory under BaFin’s February 2025 AuA update and will extend across the EU under AMLR Article 8(3).
- Scenario library with exclusion rationale: not just which typology scenarios are active, but documented reasoning for the ones that are not.
- Customer risk model: how customers are scored, what data drives the score, how the thresholds were validated, and how they tie back to the ML and TF risk assessments.
- Control mapping and review cycle: every control tied to an identified risk, with documented triggers for methodology review based on regulatory updates, business change, and examination findings.
These components are an interdependent system. A customer risk model not grounded in the risk assessment produces scores that cannot be defended. A scenario library disconnected from the business reality leads to monitoring that is irrelevant or dangerously incomplete. The methodology is the connective tissue; without it, the institution has operational parts but no intellectual foundation to tie them together.
Why It Stays Broken, and How to Fix It
If this gap is consistently cited and consequential, why does it persist? The answer lies in the structural economics of compliance investment.
Technology investment produces visible outputs (alerts, cases, reports) that can be demonstrated to regulators. Methodology documentation produces nothing visible until a regulator asks for it. It is therefore consistently the last item funded and the first item deferred. When institutions do invest, the dominant model is an annual external consultancy engagement costing somewhere between €100,000 and €500,000. This model has three failure modes that examiners see repeatedly:
- Currency: the document is accurate on the day it is produced; regulations and business models move immediately.
- Ownership: a document produced by a consultant is not internalised by the MLRO. When an examiner asks why a particular threshold was set, the person accountable can’t defend a choice they didn’t make.
- Connectivity: the consultant produces the document; the institution operates the programme; the two frequently describe different realities.
Closing the gap requires a shift from periodic artefact to living infrastructure. Three concrete moves separate institutions that survive examinations from those that don’t:
First, own the document internally. Whatever tooling or external support is used to produce it, the MLRO and compliance team must have built it, understood every choice, and be able to defend every threshold under questioning. The practical test is simple: if an examiner asks why EDD kicks in at a customer risk score of 75 rather than 70, the answer should take thirty seconds, not thirty minutes of searching for the consultant’s original working file. A methodology that cannot be explained by the person accountable for it is not a methodology; it is a liability.
Second, connect methodology to configuration. When a TM threshold changes in the system, the methodology version should update, log the justification, and trigger a governance review. When the methodology changes, it should be immediately clear which scenarios, risk-scoring rules, and CDD triggers are affected. In practice, this means the methodology document and the system configuration register reference each other by version, so a BaFin examiner asking “why is this scenario tuned this way” gets a single, traceable answer rather than two documents describing different realities.
Third, separate TF from ML explicitly. Under BaFin’s updated AuA, and under AMLR from 1 July 2027, a combined ML/TF risk assessment will not satisfy Article 8(3). In concrete terms, this means a dedicated TF threat assessment covering sanctioned jurisdictions, dual-use goods exposure, NPO customer segments, and correspondent banking flows, with its own scenario set and its own review cycle. Institutions that have not yet separated the two are already behind the line BaFin is drawing in current examinations.
Eighteen Months
The EU Anti-Money Laundering Regulation, effective 1 July 2027, turns methodology from a long-term aspiration into a near-term compliance requirement. Article 8 codifies the documented, institution-specific risk assessment; Article 8(3) makes TF separation explicit across all EU jurisdictions; Articles 20, 22, and 26 tie CDD, transaction monitoring, and ongoing monitoring intensity back to that methodology.
Eighteen months is shorter than it looks. Methodology revisions need management body approval, governance cycles consume three to six months, and thematic AMLR readiness reviews will begin well before the effective date. If the majority of EU-supervised institutions seek external methodology support simultaneously in late 2026, the available consultant capacity in the DACH region alone will not come close to meeting demand.
Two futures are forming. In the first, institutions that move now will arrive at July 2027 with a methodology they own, a compliance team that can defend it in examination, and a direct line from their risk assessment to every scenario, threshold and control their systems run. When BaFin arrives, they will be answering questions, not scrambling to reconstruct the reasoning behind a document a former consultant produced two years earlier.
In the second, institutions will do what they have always done: defer, rely on the annual consultancy cycle, and hope the examination year happens to align with a fresh delivery. They will enter the AMLR era with a methodology that describes an institution that no longer quite exists, produced by a consultant who has since moved on, filed in a SharePoint folder nobody has opened since. For those institutions, the next five years will look a lot like the last five: findings, remediation, fines, repeat.
There is a reason the gap has survived a decade of regulatory pressure, rising fines, and continuous investment in AML technology. It has survived because the industry has kept treating it as a documentation problem. It is not. It is an infrastructure problem. And infrastructure problems are not solved through periodic artefacts; they are solved through systems that keep methodology, configuration, and governance continuously aligned. The institutions that internalise this first will not just close the gap. They will stop having to reopen it every year. The brain of compliance has been scattered for a long time. The window to put it back together is finite, and it is closing.
Key Points
- Regulators consistently identify weak or undocumented AML methodology as a primary compliance failure across jurisdictions
- Enforcement actions show that operational systems fail when not anchored to a clear, defensible risk framework
- A robust methodology must connect risk assessment, customer scoring, scenarios, and controls into one coherent system
- External consultancy-driven approaches often fail due to a lack of ownership, outdated content, and weak integration
- Upcoming EU AMLR requirements will make methodology a mandatory, scrutinized component of AML programmes
Related Links
- BaFin Minimum Requirements for Risk Management MaRisk and AML Guidance
- FCA Thematic Review on AML and Financial Crime Controls 2023
- European Union Anti-Money Laundering Regulation AMLR Article 8
- FATF Guidance on Risk Based Approach for AML CFT
- OCC Enforcement Actions and Consent Orders Database
Other FinCrime Central Articles About AML Practice and the Human Factor
- The Blind Spot in Financial Crime: Why the People Who Should Be Stopping It Are Letting It Through
- Why AI Driven SAR Explosion Is Quietly Breaking Financial Intelligence
- Cracking the AML Target Operating Model Challenge
Some of FinCrime Central’s articles may have been enriched or edited with the help of AI tools. It may contain unintentional errors.
Want to promote your brand, or need some help selecting the right solution or the right advisory firm? Email us at info@fincrimecentral.com; we probably have the right contact for you.