An exclusive article by Fred Kahn
Cryptocurrency and blockchain architectures evolve rapidly, and one of the most consequential AML-related developments in recent years has been the rise of layer-2 scaling solutions, particularly rollups.These networks attempt to increase throughput, lower fees, and improve scalability beyond what base chains can support. But as these layer-2 networks grow, they also present fresh risks and challenges for anti-money laundering (AML) compliance. Criminals and illicit actors are already adapting to exploit these new layers. Compliance officers, financial crime specialists, and regulators must now contend with increasingly complex transaction layering, opaque bridging, and obfuscation techniques that stretch the limits of traditional monitoring tools. This article delves into how layer-2 networks complicate AML, why rollup architectures are attractive to money launderers, and what compliance professionals should do to stay ahead.
Table of Contents
Why rollups and layer-2 matter for money laundering
Layer-2 networks, such as optimistic rollups or zero-knowledge (ZK) rollups, operate on top of a base blockchain (layer-1) to batch or compress transactions off-chain, then submit compact proofs or summaries back to the base chain. Because of this architecture, many individual transfers are hidden from direct view on the base chain. Instead, only aggregated proofs or checkpoints are visible. That means much of the transaction detail is internal to the layer-2 environment or in off-chain data stores or rollup nodes. Criminal actors can exploit this by hiding more of their money movement from monitoring systems that only observe the base chain.
There are several reasons why launderers are increasingly interested in layer-2 networks:
- Lower fees attract high volume, which helps launderers efficiently “smurf” or split large amounts into many small transfers.
- Speed and scalability facilitate rapid transaction cycling, allowing criminals to move funds through multiple hops in seconds.
- Cross-rollup bridges and multi-chain interoperability offer pathways to frustrate traceability across ecosystems.
- Off-chain or semi-off-chain state channels, in conjunction with rollups, permit private transfers or hidden accounting layers.
- New anonymity enhancements or cryptographic tricks (e.g. private mempools, transaction batching, mixing inside rollups) amplify concealment.
From a money laundering perspective, layer-2 networks widen the space in which layering (in the AML sense) can occur. Criminals can use sequences of internal transfers, re-batching, rollup exits, bridging, and reentry into other rollups or chains to scramble provenance. The “chain of custody” of funds becomes murkier not only because of cross-chain hops, but because entire subpaths may never appear on the base chain in full detail.
Thus the growing role of layer-2 networks is not merely additive risk; it changes the topology of illicit financial flows. Compliance systems that rely exclusively on base-chain visibility become blind to many of the crucial steps in laundering chains. For compliance officers, this demands new strategies, tools, and vigilant tracking across multiple layers and bridges.
Technical pain points for AML on rollups
To understand how challenging it is to police money laundering in layer-2 systems, we examine key technical pain points from the perspective of transaction tracing, monitoring, detection, and suspicious activity reporting.
Limited visibility and compressed proofs
In many rollup systems, especially ZK rollups, the majority of transaction data is compressed into succinct proofs that are posted to the base chain. The base chain knows that “some state transitions occurred” but does not see the details of every transfer, counterparty, or routing path. Even in optimistic rollups, fraud proofs only reveal some states when challenged, but not complete transaction logs. That means compliance tools that inspect blockchain transaction graphs at layer-1 may see only the aggregated outcomes (e.g. deposits into or withdrawals from the rollup), but not the internal layering steps.
Bridge jumps and hidden jumps
Layer-2 architectures require bridges or connectors to move funds between layer-1 and layer-2, or across different rollups. Each bridging event is a potential obfuscation point. Criminals might cross from layer-1 to a rollup, engage in multiple hidden transfers there, then exit to another rollup or back to layer-1. If the bridging contracts do not retain or expose all metadata (origin address, internal route, timestamps), tracing those funds across jumps becomes far more difficult. Some bridges may be noncustodial but opaque in terms of internal routing or relayer paths.
Transaction batching and aggregation
Rollups batch many transactions into a single bundle for submission to the base chain. Within that bundle, many internal transfers occur, which are collapsed into a single proof. From the base chain perspective, you only see “rollup deposit” or “rollup withdrawal” events. The internal sequence—who sent how much to whom—is invisible. Launderers can exploit that by concealing multiple hops, cycles, and internal micro-transfers inside a batch, making detection extremely difficult unless one has deep access to rollup internals.
Off-chain messaging or state commitments
Some rollups or second-layer frameworks use off-chain messaging layers or commit state roots that rely on participants’ off-chain data. For example, side channels, watchtowers, or fraud proof networks may privately relay transaction details outside the public blockchain. If criminals control or collude with rollup node operators, they could manipulate or hide payloads. From a compliance standpoint, missing off-chain traceability breaks the chain of auditability.
High throughput and velocity
Rollups, by design, facilitate high transaction throughput. Criminals can exploit that by executing high-frequency micro-transactions, quickly shifting balances, and generating noisy background traffic. That increases the false positive noise and makes suspicious flows harder to spot. Rapid cycling of funds inside the rollup shortens dwell time on any single address, complicating pattern detection.
Anonymous or pseudonymous internal addresses
Within a rollup environment, users may deploy multiple pseudonymous internal addresses that are rarely linked to off-rollup identity. Because identities are not necessarily tied at the rollup level, criminals can rapidly rotate addresses, reuse mixing strategies, or employ internal address stealth techniques to avoid pattern linkage. Conventional KYC linking is harder when internal addresses are anonymous to external observers.
Smart contract composability
Many rollups support smart contract platforms, enabling decentralized exchanges, automated market makers, lending and borrowing, yield farming, and other composable protocols. Criminals can integrate mixing, swapping, flash loans, synthetic assets, and cross-protocol arbitrage in a single laundering chain inside a rollup. That composability magnifies layering complexity: one user can sweep via a DEX, cross via a bridge, swap stablecoins, borrow funds, repay, and exit — all inside a rollup maze.
Time delays and finality uncertainty
Optimistic rollups depend on challenge periods (e.g., seven days or longer) to verify fraud proofs. During that window, transaction status is tentative. Funds might be shifted, revoked, or reorged within the rollup’s internal history. This uncertainty can allow malicious actors to exploit reversible states, reorg transfers, or stealth exits before finalization, further complicating tracking.
Because of these pain points, AML monitoring cannot rely solely on base chain data or simplified transaction graphs. Instead, compliance systems must integrate cross-layer observability, deeper rollup node access, bridging metadata, contract analytics, and refined heuristics.
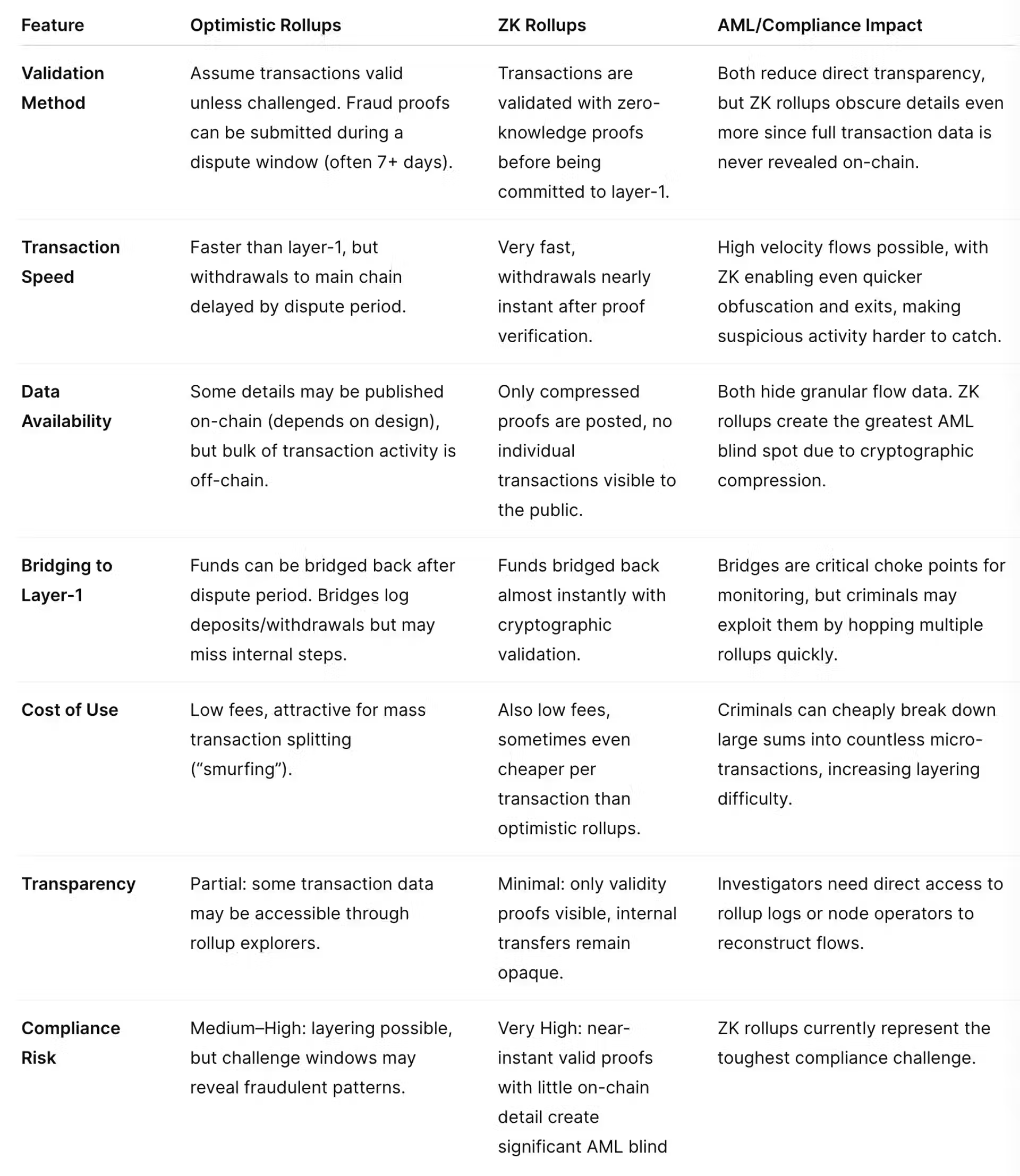
Level-2 roll-up comparison
What compliance officers should track and build
Faced with these challenges, compliance officers must proactively expand their monitoring scope, adopt new tooling, and enforce rigorous controls. Below are key areas to track, metrics to monitor, and strategies to pursue.
Full stack traceability
Compliance tooling must ingest not just base layer-1 blockchain data but also rollup internal logs, state transition proofs, off-chain aggregator data, and bridging metadata. Wherever possible, auditors or compliance teams should seek access to rollup nodes, official block explorers, or APIs that expose internal transactions. The goal is reconstructing internal chains of transfers that standard chain viewers do not show.
Bridge metadata compliance
Bridges are one of the most critical choke points. Compliance officers should demand or negotiate with bridge providers to log and retain metadata: origin address, timestamp, internal route, relayer addresses, transaction hashes, and contractual call trees. Bridge operators should be contractually obligated in service agreements to share or escrow that data for regulatory or audit review. Tracking the volume, frequency, and recurrence of bridging by particular addresses can signal risky patterns (e.g. repeated rollup jumps, frequent reentry).
Internal transfer velocity and churning rate
Because criminals exploit rapid cycling, compliance teams should monitor address-level velocity metrics: how many internal transfers per unit time, average balance dwell time, and churn ratios (incoming vs outgoing micro transactions). Abnormally high internal activity inside a rollup or sudden bursts of transfer volume warrant alerting. Dwell times much shorter than typical user behavior are a red flag.
Address reuse and rotation detection
Identify internal address reuse or rapid address rotation. If a user spins up dozens of new internal addresses in a short span and moves balances among them, that may be an obfuscation tactic. Cluster these internal addresses using heuristics, graph models, or anomaly detection, and track cluster behavior rather than individual addresses.
Composability flow graphs
Inside rollups, criminals may combine multiple protocols in one laundering chain. Compliance tooling should parse and map composability flows. For example, a suspicious flow might go: internal wallet → DEX swap → synthetic asset → bridge → yield vault → exit. Represent such flows as directed graphs and score complexity, cross-protocol hops, and mixing interactions.
Bridge path frequency and cross-rollup circuits
Monitor how frequently individual addresses or clusters cross between rollups or chains. Unusually complex circuits — e.g. rollup A → chain → rollup B → rollup C → chain — may be designed to foil traceability. Compliance systems should flag overly circuitous paths beyond typical user behavior.
Exit to fiat gateways or regulated endpoints
Eventually, criminals often convert their crypto proceeds to fiat via exchanges, OTC desks, or regulated intermediaries. Monitoring the endpoints where rollup funds exit is critical. Compliance officers should focus on identifying known bridges to exchanges, gateways, or on-ramps, and crossmatch deposit addresses or flow links to those entities. If internal rollup flows funnel disproportionately to a specific exit address, that is suspicious.
Threshold behavior and structuring inside rollups
Just as structuring is used in fiat systems to avoid reporting thresholds, criminals may subdivide large transfers into many small internal transfers to avoid triggering automated alerts. Compliance systems should treat aggregated transfers, summing incoming and outgoing transfers over windows to detect structured flows even below individual thresholds. For example, if an address transfers 0.9 ETH ten times in an hour instead of a single 9 ETH transfer, the system should detect the cumulative pattern.
Temporal pattern anomalies
Because layering strategies often involve time manipulation, compliance tools should detect temporal inconsistencies — e.g. transfers occurring at highly regular intervals, burst patterns, or time gaps that match known laundering scripts. Sudden bursts of internal transfers after extended dormancy, or precisely spaced cycles, can signal algorithmic laundering.
Cluster scoring and suspicious cluster prioritization
Instead of focusing only on individual addresses, compliance systems should cluster internal addresses on behavioral similarity and flow patterns. Each cluster can receive a risk score based on internal activity complexity, bridging behavior, composability hops, velocity, and exit proximity. Teams should prioritize clusters with high composite scores for manual review.
Alerts and case escalation rules
Define alert thresholds specific to rollup environments: internal rate limits, cross-layer jumps, churning thresholds, composability complexity thresholds, bridging frequency, and cumulative transfer sums. Escalate clusters or flows that cross multiple thresholds for investigation and suspicious activity reporting.
Cooperation agreements and data sharing
Many rollups are operated by third-party teams or developers rather than centralized exchanges. Compliance offices should seek formal cooperation with rollup operators, developers, and bridge providers. This might include data sharing memoranda, access APIs, or audit channels. Having buy-in from protocol operators is essential because they hold the keys to internal visibility.
Continuous model improvement and machine learning
Because illicit actors adapt, compliance officers should employ machine learning, anomaly detection systems, graph neural networks, and self-supervised learning models to detect emergent laundering behavior. Networks that learn from evolving patterns inside rollups will outperform static rule sets. Synthetic AML transaction generators may help train models on layered flows across rollups.
Audit trails and reconstruction workflows
Whenever a suspicious cluster is detected, compliance teams must be able to reconstruct the full path: from base chain deposit, rollup bridging, internal steps, bridging exit, to fiat conversion. That end-to-end trail is key to effective suspicious activity reporting and law enforcement referrals.
Risk governance and regulatory alignment in the rollup era
Technical monitoring is not enough. Compliance officers must also ensure sound governance, policy treatment, and alignment with evolving regulation.
Updating risk assessments and internal policies
Financial crime risk assessments (FCRAs) and AML frameworks should explicitly incorporate layer-2 risks. Policies and internal procedure manuals must address rollups, bridges, cross-layer flows, and internal transfer monitoring. Compliance teams should classify various rollups and bridges by risk tiers, considering factors like centralization, privacy features, node operator transparency, and bridge metadata pledges.
Third-party risk and protocol vetting
When a business interacts with a particular rollup or bridge (e.g. deposits or integrates that protocol), it should perform third-party risk due diligence: evaluate the operator’s commitment to transparency, data retention, compliance cooperation, auditability, and history of vulnerabilities or illicit usage. The compliance function should provide red lines, for example withholding support for rollups that provide no internal audit API or governance oversight.
Regulatory engagement and standard setting
Compliance officers should engage actively with regulators and industry groups to push for standards, guidelines, or regulation covering layer-2 systems, rollup internal traceability, bridge metadata rules, and reporting norms. Without regulatory pressure, many rollup operators may neglect AML obligations. Compliance teams should monitor evolving laws, such as those around virtual assets, digital asset service providers, and cross-border funds transfer regulations.
Escalating to legal and law enforcement
When suspicious clusters are uncovered, compliance teams need processes to escalate to legal and law enforcement with complete reconstructed trails. Because layering across rollups is novel, teams should invest in digital forensic capability, cross-protocol intelligence, and case packages that document internal rollup trails. Partnerships with blockchain forensics firms or law enforcement tracing specialists may be needed.
Training and awareness
Compliance staff, investigators, and AML analysts must be trained in rollup architectures, bridging logic, zero-knowledge proofs, and advanced chain analysis. Understanding how rollups work is foundational to detecting abuses. Without awareness, red flags may be missed.
Monitoring evolving law and regulation
Many jurisdictions are now updating or proposing laws regulating virtual assets, crypto — including obligations on custody providers, exchanges, and digital asset service providers (VASPs). Compliance officers must stay abreast of such regimes (e.g. travel rule, beneficial ownership of wallets, cross-border disclosure). Some governments may impose rollup operator registration or internal traceability duties. Compliance teams should position themselves to adapt to those incoming rules.
What the future may bring and strategic posture
As criminals adapt, so too must compliance strategies. In the coming years, we anticipate:
- More private rollup modes or confidentiality primitives (e.g. zk-SNARK mixes, private transactions) that further reduce external visibility.
- Cross-rollup aggregators or routers that shuffle funds across many networks in one atomic transaction, making path reconstruction harder.
- Advanced mixing services built inside rollups (e.g. pay-out mixers, zero-knowledge mixers internal to layer-2).
- Layer-2s with selective data disclosure options, where only authorized parties or auditors can view internal state.
- Collaboration between forensic analytics firms and rollup node providers to embed traceability from the start.
- Regulatory requirements for mandatory rollup audit APIs, metadata retention, and bridging logs.
- Convergence between artificial intelligence, graph neural networks, and real-time cross-layer scoring systems to flag advanced laundering schemes.
Given that layer-2 networks are still in evolution, compliance officers are at a window of opportunity: to shape standards, demand transparency, upgrade tooling, and embed AML awareness into emerging protocols. Those who fall behind risk playing catch-up after illicit actors already exploit opaque systems.
Related Links
- FATF official guidance on virtual assets and VASP regulation
- European Union regulation on Markets in Crypto-Assets (MiCA)
- U.S. FinCEN rules on digital asset service providers (VASPs)
- Basel Committee principles on digital assets and risk governance
- National regulator or FIU statements on crypto AML
Other FinCrime Central Article About Latest Market Practice in Crypto
- The Vital Role of Transaction Monitoring in Crypto Compliance
- The Ultimate Guide to AML in Crypto: What Investors Need to Know
- Seizing the AML Services and Advisory Boom in 2025
Some of FinCrime Central’s articles may have been enriched or edited with the help of AI tools. It may contain unintentional errors.
Want to promote your brand, or need some help selecting the right solution or the right advisory firm? Email us at info@fincrimecentral.com; we probably have the right contact for you.













