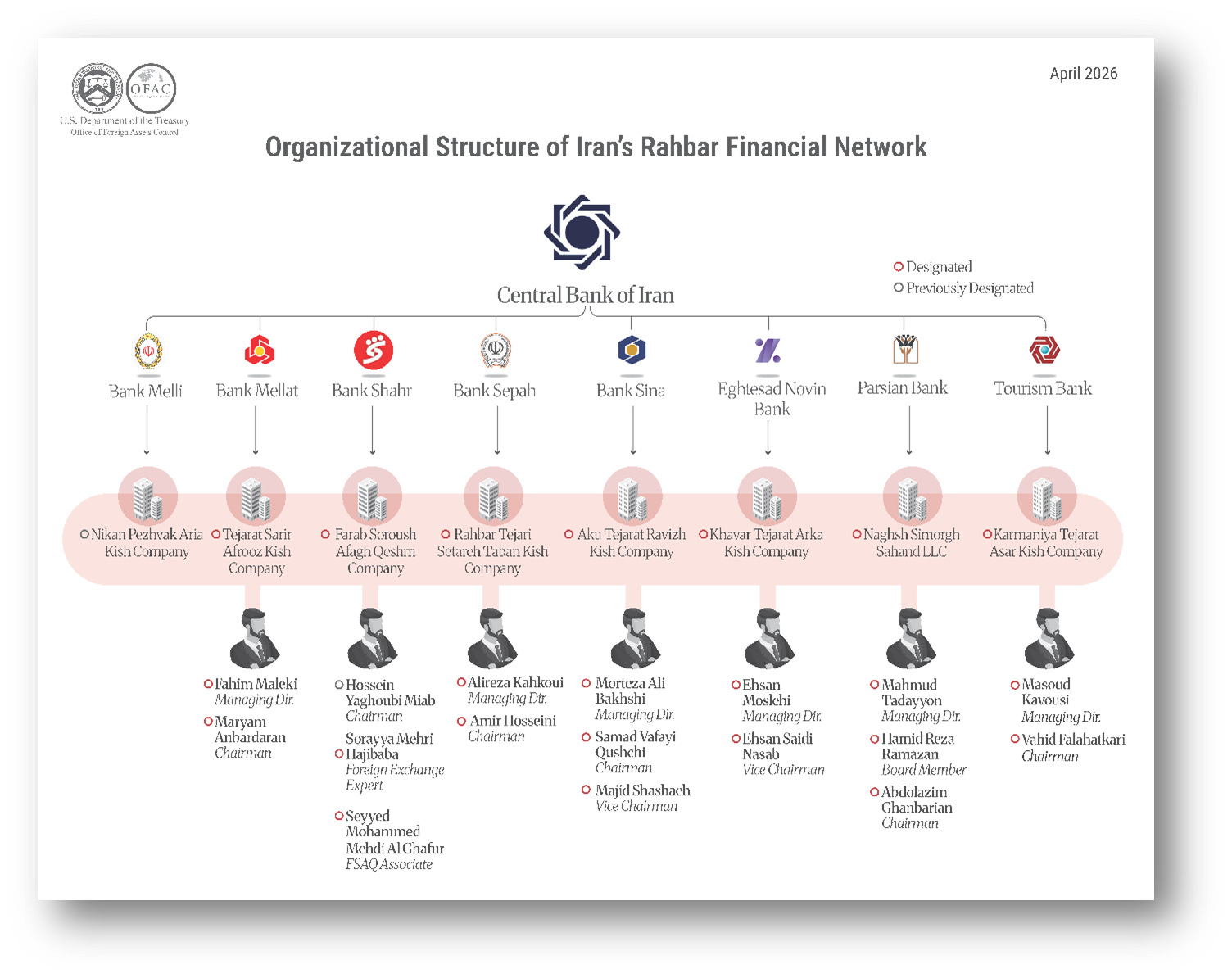
The United States Department of the Treasury recently announced the designation of a massive financial network that leveraged digital assets to bypass international trade restrictions. This enforcement action targets a sophisticated web of money launderers and front companies that successfully moved over 150 million dollars to benefit Iranian state interests. By utilizing various cryptocurrency exchanges and obfuscation techniques, the sanctioned entities attempted to hide the origin and destination of funds destined for sanctioned military and political groups. Federal authorities emphasize that this crackdown is part of a broader strategy to neutralize the digital loopholes used by adversarial regimes to fund destabilizing activities. The Treasury Department remains committed to monitoring the evolving intersection of decentralized finance and illicit state sponsorship to protect the integrity of the global financial system.
Table of Contents
Treasury Crackdown on Crypto Laundering
The recent intervention by the Office of Foreign Assets Control highlights a critical shift in how federal regulators approach the oversight of virtual asset service providers. This specific network operates by utilizing a series of intermediary wallets and shell companies located across multiple jurisdictions to facilitate the movement of millions of dollars. The primary focus of these operations was to convert local Iranian currency into stablecoins and other liquid digital assets, which could then be transferred across borders without triggering traditional banking alerts. Investigators discovered that the network relied on a small group of highly technical facilitators who managed the private keys and exchange accounts necessary to maintain the flow of capital. These individuals acted as the connective tissue between the sanctioned state and the international crypto markets, proving that digital currencies have become a preferred tool for high-stakes sanctions evasion. The scale of this 150 million dollar operation demonstrates that the volume of illicit finance within the crypto ecosystem is significant and requires aggressive, data-driven enforcement. Treasury officials noted that the designated entities were not merely peripheral players but were central to the economic survival of specific Iranian programs that are currently under heavy international pressure. This action sends a clear signal to all virtual asset participants that ignorance of customer identity is no longer an excuse for facilitating prohibited transactions.
The complexity of the network involved several layers of obfuscation designed to frustrate blockchain analysis tools. By using a mix of centralized exchanges and peer-to-peer lending platforms, the facilitators were able to break the audit trail of the funds. Once the assets were converted into digital form, they were often tumbled or mixed through various services before being settled into accounts that appeared to be legitimate commercial enterprises. These front companies claimed to be involved in the trade of consumer goods or agricultural products, providing a veneer of legality to the underlying financial transfers. However, forensic accounting revealed that the timing and volume of these transactions did not align with actual physical trade flows. Instead, the money was being redirected to support the procurement of sensitive technologies and the financing of regional proxies. The coordination between the Department of the Treasury and international partners was essential in mapping out these nodes, as many of the physical operations were based outside of the United States. This international cooperation is vital because the decentralized nature of blockchain technology allows bad actors to exploit regulatory gaps in countries with weaker anti-money laundering frameworks. The enforcement action serves as a reminder that the global community is closing the net on those who believe that digital anonymity provides a permanent shield from legal consequences.
Operational Tactics of Sanctioned Virtual Networks
Understanding the specific methods used by the Iranian-linked network reveals the vulnerabilities currently present in the global crypto infrastructure. One of the most common tactics employed by these groups involves the use of nested exchanges, where a smaller, less regulated exchange uses the liquidity of a larger, compliant platform to process transactions. This allows the illicit actors to piggyback on the reputation of major financial hubs while avoiding the stringent know your customer requirements that those hubs usually enforce. In this case, several of the sanctioned individuals managed accounts on major platforms using forged or stolen identities, effectively tricking the service providers into thinking the funds were coming from legitimate retail investors. The use of virtual private networks and other privacy-enhancing technologies further complicated the efforts of law enforcement to geolocate the actors. Despite these hurdles, the integration of advanced on-chain monitoring and traditional intelligence gathering allowed the Treasury to pin down the exact individuals responsible for the 150 million dollar scheme.
Furthermore, the network frequently rotated its wallet addresses to prevent any single address from accumulating a balance large enough to attract immediate attention from compliance teams. This strategy, often referred to as peeling, involves sending a small portion of funds to a destination while moving the remainder to a new, fresh wallet. By repeating this process hundreds of times, the launderers create a massive web of transactions that can be difficult for human analysts to parse quickly. The Treasury Department’s report indicates that this Iranian network was particularly adept at this technique, using automated scripts to manage the movement of assets across thousands of different addresses. This level of technical sophistication suggests that state-sponsored laundering operations are becoming increasingly professionalized, often mirroring the capabilities of legitimate financial technology firms. To combat this, regulators are now encouraging exchanges to implement more robust behavioral monitoring systems that can detect the patterns of peeling and other automated laundering signatures. The focus is shifting from simply blacklisting known addresses to identifying the underlying behaviors that characterize illicit activity. This proactive approach is necessary to keep pace with the rapid innovation in the crypto sector and to ensure that the tools of financial freedom are not permanently co-opted by those seeking to cause global harm.
Regional Impacts and Regulatory Responses
The disruption of this 150 million dollar network has significant implications for the regional stability of the Middle East and the broader global economy. By cutting off a major artery of illicit funding, the United States is effectively reducing the capacity of the Iranian government to finance its regional ambitions and procure restricted materials. This action does not occur in a vacuum but is part of a multifaceted pressure campaign that includes diplomatic, economic, and cyber components. Other countries in the region are watching these developments closely, as many are also struggling with the rise of crypto-based crime. The success of this specific operation provides a roadmap for other nations to follow in terms of how to combine blockchain forensics with traditional financial investigations. It also highlights the need for a unified global standard for crypto regulation, as the current patchwork of laws creates safe havens for launderers.
In response to these threats, the Financial Action Task Force has been updating its guidance to emphasize that virtual asset service providers must be held to the same standards as traditional banks. This includes the implementation of the travel rule, which requires the exchange of sender and receiver information for large transactions. While the Iranian network was able to bypass some of these controls through deceptive practices, the increased adoption of these standards makes it much harder for such large-scale operations to persist indefinitely. Many of the nodes in the recently sanctioned network were located in jurisdictions that have recently committed to improving their financial oversight, suggesting that the space for these actors to operate is shrinking. The Department of the Treasury has also hinted that further designations are likely as more data is extracted from the seized servers and analyzed. This ongoing effort is intended to create a hostile environment for illicit financiers, forcing them into more expensive and less efficient methods of moving money. The ultimate goal is to make the cost of sanctions evasion so high that it becomes an unviable strategy for state actors. As the digital economy continues to grow, the battle between regulators and launderers will remain a central theme in international relations, with crypto being the primary battleground.
Future Outlook for Digital Asset Compliance
Looking ahead, the landscape of digital asset compliance will be defined by an even greater integration of technology and law enforcement. The 150 million dollar seizure related to the Iranian network is a milestone, but it also underscores the persistence of the threat. Regulators are now looking at how to address the risks posed by decentralized finance protocols and non-custodial wallets, which do not have a central authority that can be served with a subpoena. While the network in this case largely used centralized exchanges, the transition to decentralized platforms is a logical next step for savvy launderers. This will require new types of regulatory tools, such as the potential for smart contract audits and the monitoring of liquidity pools for suspicious movements. The conversation is also moving toward the role of stablecoins, which have become the preferred medium of exchange for many of these networks due to their price stability and high liquidity.
As governments around the world develop their own central bank digital currencies, the lessons learned from the Iranian crypto network will be invaluable. These new forms of state-backed digital money will likely include built-in compliance features that make the types of laundering seen in this case much more difficult. In the meantime, the private sector must step up its efforts to share information about emerging threats. Groups like the Crypto Defenders Alliance and other industry associations are already working to create shared databases of suspicious addresses and actors. This collaborative approach is essential because the speed of crypto transactions requires a near-real-time response from the compliance community. The Iranian case proves that when the government and the private sector work together, it is possible to identify and dismantle even the most complex financial networks. The future of financial integrity depends on our ability to maintain this momentum and to ensure that the digital frontier is a place of innovation and growth rather than a sanctuary for crime. By continuing to target the infrastructure of illicit finance, the international community can ensure that digital assets serve the common good and do not become a tool for the destruction of global order. The 150 million dollar enforcement action is not the end of the story but rather a significant chapter in the ongoing effort to secure the global financial system in the 21st century.
Key Points
- The Treasury Department designated a network responsible for moving over 150 million dollars for Iranian interests.
- Illicit actors used a combination of shell companies and crypto exchanges to hide the flow of funds.
- Blockchain forensics played a critical role in identifying the deceptive peeling and layering tactics.
- The enforcement action targets both the financial facilitators and the front companies used in the scheme.
- Ongoing international cooperation is necessary to close the regulatory gaps exploited by state-sponsored launderers.
Related Links
- OFAC Sanctions Search and Resource Center
- FATF Guidance on Virtual Assets and Virtual Asset Service Providers
- Financial Crimes Enforcement Network Crypto Resource Hub
- Department of Justice Digital Asset Enforcement Actions
Other FinCrime Central Articles About Sanctions on Iran
- Danish FSA Hits Merex International Over High Risk Iran Transfers
- Escalated Digital Asset Outflows from Iranian Platforms During Conflict
- Digital Asset Risks and Sanctions On Iran Explode in Castellum AI Annual Review
Source: US Treasury
Some of FinCrime Central’s articles may have been enriched or edited with the help of AI tools. It may contain unintentional errors.
Want to promote your brand, or need some help selecting the right solution or the right advisory firm? Email us at info@fincrimecentral.com; we probably have the right contact for you.